攻防世界 reverse Windows_Reverse1
2021-01-16 03:13
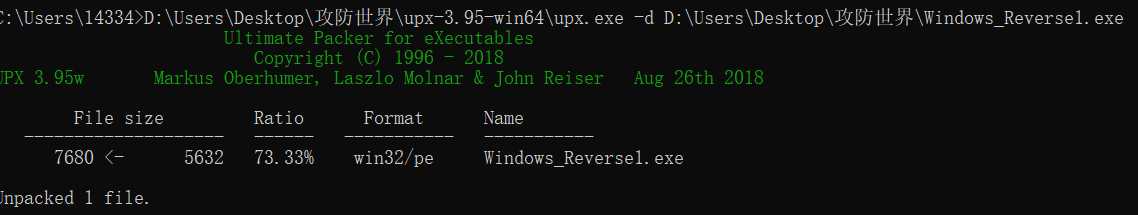
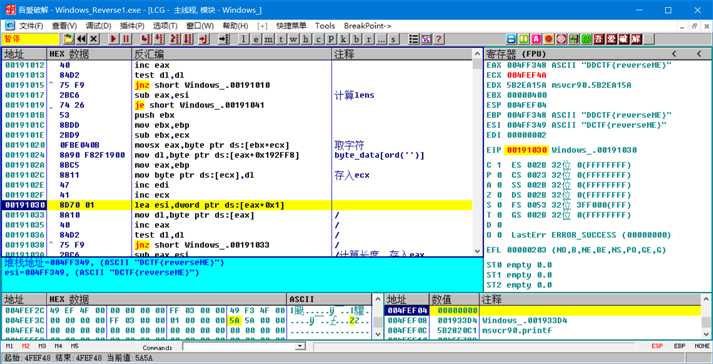
标签:return spl gif display env ret span input sub Windows_Reverse1 2019_DDCTF 查壳 脱壳 脱壳后运行闪退,(或许需要修复下IAT??),先IDA 静态分析一下 关键函数sub_401000 应该就是一个简单的替换算法,然后程序将结果与“DDCTF{reverseME}“进行比较。 接下来进行动态调试dump出置换数组 wp: flag{ZZ[JX#,9(9,+9QY!} 攻防世界 reverse Windows_Reverse1 标签:return spl gif display env ret span input sub 原文地址:https://www.cnblogs.com/DirWang/p/12230774.html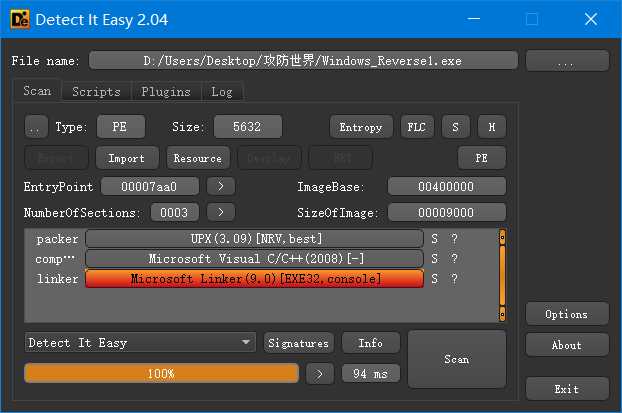
int __cdecl main(int argc, const char **argv, const char **envp)
{
char v4; // [esp+4h] [ebp-804h]
char v5; // [esp+5h] [ebp-803h]
char v6; // [esp+404h] [ebp-404h]
char Dst; // [esp+405h] [ebp-403h]
v6 = 0;
memset(&Dst, 0, 0x3FFu);
v4 = 0;
memset(&v5, 0, 0x3FFu);
printf("please input code:");
scanf("%s", &v6);
sub_401000(&v6);
if ( !strcmp(&v4, "DDCTF{reverseME}") )
printf("You‘ve got it!!%s\n", &v4);
else
printf("Try again later.\n");
return 0;
}


unsigned int __cdecl sub_401000(const char *a1)
{
_BYTE *v1; // ecx
unsigned int v2; // edi
unsigned int result; // eax
int v4; // ebx
v2 = 0;
result = strlen(a1);
if ( result )
{
v4 = a1 - v1;
do
{
*v1 = byte_402FF8[(char)v1[v4]];
++v2;
++v1;
result = strlen(a1);
}
while ( v2 result );
}
return result;
}
# -*- coding: UTF-8 -*-
hexData=[
0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0xF8, 0xAE, 0x1D, 0x3E, 0x07, 0x51, 0xE2, 0xC1,
0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0xFE, 0xFF, 0xFF, 0xFF, 0x01, 0x00, 0x00, 0x00,
0x7E, 0x7D, 0x7C, 0x7B, 0x7A, 0x79, 0x78, 0x77, 0x76, 0x75, 0x74, 0x73, 0x72, 0x71, 0x70, 0x6F,
0x6E, 0x6D, 0x6C, 0x6B, 0x6A, 0x69, 0x68, 0x67, 0x66, 0x65, 0x64, 0x63, 0x62, 0x61, 0x60, 0x5F,
0x5E, 0x5D, 0x5C, 0x5B, 0x5A, 0x59, 0x58, 0x57, 0x56, 0x55, 0x54, 0x53, 0x52, 0x51, 0x50, 0x4F,
0x4E, 0x4D, 0x4C, 0x4B, 0x4A, 0x49, 0x48, 0x47, 0x46, 0x45, 0x44, 0x43, 0x42, 0x41, 0x40, 0x3F,
0x3E, 0x3D, 0x3C, 0x3B, 0x3A, 0x39, 0x38, 0x37, 0x36, 0x35, 0x34, 0x33, 0x32, 0x31, 0x30, 0x2F,
0x2E, 0x2D, 0x2C, 0x2B, 0x2A, 0x29, 0x28, 0x27, 0x26, 0x25, 0x24, 0x23, 0x22, 0x21, 0x20, 0x00,
0x01, 0x00, 0x00, 0x00, 0x90, 0x19, 0x9F, 0x00, 0xA8, 0x2C, 0x9F, 0x00, 0x00, 0x00, 0x00, 0x00,
0x00, 0x00, 0x00, 0x00 ]
str=‘DDCTF{reverseME}‘
flag=‘‘
for i in range(len(str)):
flag+=chr(hexData[ord(str[i])])
print(‘flag{‘+flag+‘}‘)
文章标题:攻防世界 reverse Windows_Reverse1
文章链接:http://soscw.com/index.php/essay/42530.html