CTFshow-萌新赛逆向_签退
2021-04-09 02:27
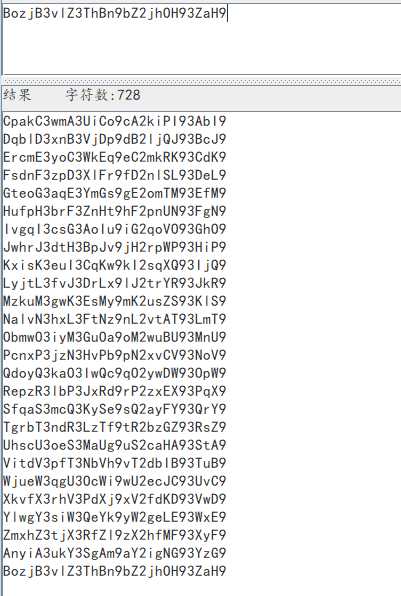
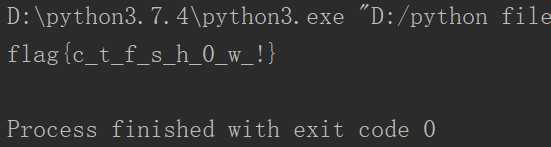
标签:使用 lambda com byte replace for odi UNC supper 查看题目信息 下载re3.pyc文件 使用uncompyle把re3.pyc反编译为re3.py 查看re3.py文件 文件分析在如上 首先使用凯撒密码进行解密 把解密后的密文写入base.txt文件中 使用脚本进行解密 成功拿到flag 附上解密脚本 CTFshow-萌新赛逆向_签退 标签:使用 lambda com byte replace for odi UNC supper 原文地址:https://www.cnblogs.com/anweilx/p/12443932.html
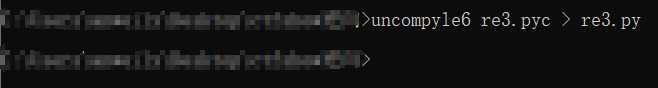
uncompyle6 re3.pyc > re3.py
# uncompyle6 version 3.6.4
# Python bytecode 2.7 (62211)
# Decompiled from: Python 2.7.15 (v2.7.15:ca079a3ea3, Apr 30 2018, 16:30:26) [MSC v.1500 64 bit (AMD64)]
# Embedded file name: re3.py
# Compiled at: 2020-03-06 17:43:28
import string
c_charset = string.ascii_uppercase + string.ascii_lowercase + string.digits + ‘()‘
flag = ‘BozjB3vlZ3ThBn9bZ2jhOH93ZaH9‘ #这个是最后输出的密文
def encode(origin_bytes): #这个函数是base64加密
c_bytes = [ (‘{:0>8}‘).format(str(bin(b)).replace(‘0b‘, ‘‘)) for b in origin_bytes ]
resp = ‘‘
nums = len(c_bytes) // 3
remain = len(c_bytes) % 3
integral_part = c_bytes[0:3 * nums]
while integral_part:
tmp_unit = (‘‘).join(integral_part[0:3])
tmp_unit = [ int(tmp_unit[x:x + 6], 2) for x in [0, 6, 12, 18] ]
resp += (‘‘).join([ c_charset[i] for i in tmp_unit ])
integral_part = integral_part[3:]
if remain:
remain_part = (‘‘).join(c_bytes[3 * nums:]) + (3 - remain) * ‘0‘ * 8
tmp_unit = [ int(remain_part[x:x + 6], 2) for x in [0, 6, 12, 18] ][:remain + 1]
resp += (‘‘).join([ c_charset[i] for i in tmp_unit ]) + (3 - remain) * ‘.‘
return rend(resp) #这个代码说明先进行base64加密,然后进行凯撒加密
def rend(s):
def encodeCh(ch): #这个函数是凯撒加密
f = lambda x: chr((ord(ch) - x + 2) % 26 + x)
if ch.islower():
return f(97)
if ch.isupper():
return f(65)
return ch
return (‘‘).join(encodeCh(c) for c in s)
# okay decompiling re3.pyc
#! /usr/bin/env python
# _*_ coding:utf-8 _*_
import base64
filename = "base64.txt"
f = open(filename,‘r‘)
while True:
text_base =f.readline()
if not text_base:
break
else:
text_str = str(base64.b64decode(text_base))
if "flag" in text_str:
text_str =text_str.replace("‘","").replace("b","")
print(text_str)