使用Spring Security登录认证,通过Oauth2.0开发第三方授授权访问资源项目详解
2021-04-02 06:28
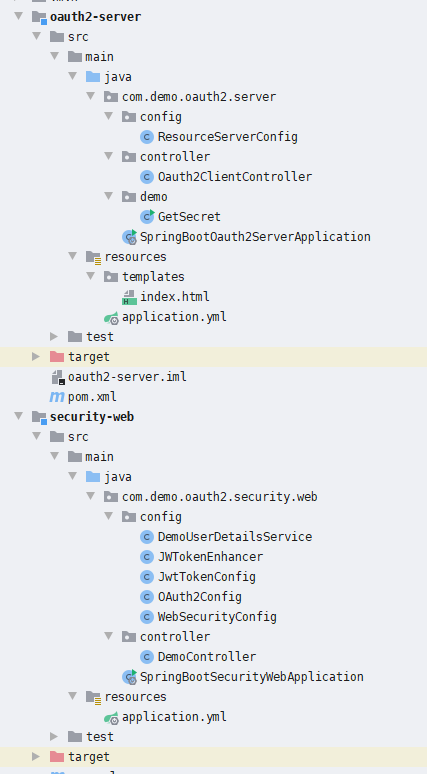
标签:用户访问 dap character repo err load htm html implicit OAuth 2.0提供者机制负责公开OAuth 2.0受保护的资源。该配置包括建立可独立或代表用户访问其受保护资源的OAuth 2.0客户端。提供者通过管理和验证用于访问受保护资源的OAuth 2.0令牌来实现。在适用的情况下,提供商还必须提供用户界面,以确认客户端可以被授权访问受保护资源(即确认页面)。 OAuth 2.0常见的有如下四种授权模式,(主要参考自 阮一峰 OAuth 2.0 的四种方式): Html演示页面地址为:http://localhost:8081/oauth2-server/index,授权访问效果如下,授权后会返回相应的token: 项目结构如下: 建表语句: pom依赖: security-web: 用于用户的认证,根据用户的用户名和密码进行认证并用于获得授权码和获取JWT token的服务,主要配置如下: GetSecret (获取Header以及加密后的密码): WebSecurityConfig OAuth2Config oauth2-server: 主要用于授权认证后的资源访问,使用的是授权码授权模式(这也是最常见的Oauth2.0的模式),主要资源配置如下: 使用Spring Security登录认证,通过Oauth2.0开发第三方授授权访问资源项目详解 标签:用户访问 dap character repo err load htm html implicit 原文地址:https://www.cnblogs.com/charlypage/p/13496423.html1.OAuth 2.0简介
2.OAuth 2.0的四种授权模式
3.使用授权码模式获得JWTtoken令牌Demo项目演示
client_id: demo-client
client_secret: demo-secret (数据表中需要加密)
// 登录页访问地址
http://localhost:8080/login
用户名: admin
密码: 123456
// 资源页访问地址
http://localhost:8081/oauth2-server/login
// 授权访问地址
http://localhost:8080/oauth/authorize?client_id=demo-client&response_type=code&redirect_uri=http://localhost:8081/oauth2-server/login
4.项目结构以及相关代码配置
CREATE TABLE `oauth_client_details` (
`client_id` varchar(256) CHARACTER SET utf8mb4 COLLATE utf8mb4_general_ci NOT NULL,
`resource_ids` varchar(256) CHARACTER SET utf8mb4 COLLATE utf8mb4_general_ci NULL DEFAULT NULL,
`client_secret` varchar(256) CHARACTER SET utf8mb4 COLLATE utf8mb4_general_ci NULL DEFAULT NULL,
`scope` varchar(256) CHARACTER SET utf8mb4 COLLATE utf8mb4_general_ci NULL DEFAULT NULL,
`authorized_grant_types` varchar(256) CHARACTER SET utf8mb4 COLLATE utf8mb4_general_ci NULL DEFAULT NULL,
`web_server_redirect_uri` varchar(256) CHARACTER SET utf8mb4 COLLATE utf8mb4_general_ci NULL DEFAULT NULL,
`authorities` varchar(256) CHARACTER SET utf8mb4 COLLATE utf8mb4_general_ci NULL DEFAULT NULL,
`access_token_validity` int(11) NULL DEFAULT NULL,
`refresh_token_validity` int(11) NULL DEFAULT NULL,
`additional_information` varchar(4096) CHARACTER SET utf8mb4 COLLATE utf8mb4_general_ci NULL DEFAULT NULL,
`autoapprove` varchar(256) CHARACTER SET utf8mb4 COLLATE utf8mb4_general_ci NULL DEFAULT NULL,
PRIMARY KEY (`client_id`) USING BTREE
) ENGINE = InnoDB CHARACTER SET = utf8mb4 COLLATE = utf8mb4_general_ci ROW_FORMAT = Dynamic;
INSERT INTO `oauth_client_details` VALUES (‘demo-client‘, NULL, ‘$2a$10$jr6DMjq2pRS1pa8vGvgdUewJTLXyHazOIgG5OrotSVhqhTgoCx1m.‘, ‘all‘, ‘authorization_code,refresh_token‘, ‘http://localhost:8081/oauth2-server/login‘, NULL, 3600, 36000, NULL, ‘1‘);
public class GetSecret {
private static final String APP_KEY = "demo-client";
private static final String SECRET_KEY = "demo-secret";
public static void main(String[] args){
System.out.println("secret: "+new BCryptPasswordEncoder().encode("demo-secret"));
System.out.println("getHeader: "+getHeader());
}
/**
* 构造Basic Auth认证头信息
*
* @return
*/
private static String getHeader() {
String auth = APP_KEY + ":" + SECRET_KEY;
byte[] encodedAuth = Base64.encodeBase64(auth.getBytes(Charset.forName("US-ASCII")));
String authHeader = "Basic " + new String(encodedAuth);
return authHeader;
}
}
@EnableWebSecurity
public class WebSecurityConfig extends WebSecurityConfigurerAdapter {
@Bean
public PasswordEncoder passwordEncoder() {
return new BCryptPasswordEncoder();
}
@Bean
@Override
public AuthenticationManager authenticationManagerBean() throws Exception {
return super.authenticationManagerBean();
}
/**
* 允许匿名访问所有接口 主要是 oauth 接口
* @param http
* @throws Exception
*/
@Override
protected void configure(HttpSecurity http) throws Exception {
http.formLogin()
.and()
.authorizeRequests()
.antMatchers("/**").permitAll();
}
}
@Configuration
@EnableAuthorizationServer
public class OAuth2Config extends AuthorizationServerConfigurerAdapter {
@Autowired
@Qualifier("demoUserDetailsService")
public UserDetailsService demoUserDetailsService;
@Autowired
private DataSource dataSource;
@Autowired
private AuthenticationManager authenticationManager;
@Autowired
private PasswordEncoder passwordEncoder;
@Autowired
private TokenStore jwtTokenStore;
@Autowired
private JwtAccessTokenConverter jwtAccessTokenConverter;
@Autowired
private TokenEnhancer jwtTokenEnhancer;
@Override
public void configure(final AuthorizationServerEndpointsConfigurer endpoints) throws Exception {
/**
* jwt 增强模式
*/
TokenEnhancerChain enhancerChain = new TokenEnhancerChain();
List@Configuration
@EnableResourceServer
@EnableGlobalMethodSecurity(prePostEnabled = true)
public class ResourceServerConfig extends ResourceServerConfigurerAdapter {
@Bean
public TokenStore jwtTokenStore() {
return new JwtTokenStore(jwtAccessTokenConverter());
}
@Bean
public JwtAccessTokenConverter jwtAccessTokenConverter() {
JwtAccessTokenConverter accessTokenConverter = new JwtAccessTokenConverter();
accessTokenConverter.setSigningKey("demo");
accessTokenConverter.setVerifierKey("demo");
return accessTokenConverter;
}
@Autowired
private TokenStore jwtTokenStore;
@Override
public void configure(ResourceServerSecurityConfigurer resources) throws Exception {
resources.tokenStore(jwtTokenStore);
}
@Override
public void configure(HttpSecurity http) throws Exception {
http.authorizeRequests().antMatchers("/login").permitAll();
}
}
5.GitHub项目地址:
https://github.com/fengcharly/spring-boot-oauth2
文章标题:使用Spring Security登录认证,通过Oauth2.0开发第三方授授权访问资源项目详解
文章链接:http://soscw.com/index.php/essay/71280.html